mirror of
https://github.com/nspcc-dev/neofs-rest-gw.git
synced 2026-04-17 13:38:05 +00:00
Define what we expect to sign #6
Labels
No labels
I2
I3
I3
I4
S2
S3
S3
S4
U0
U1
U2
U3
U3
U3
U4
blocked
bug
config
documentation
enhancement
feature
go
help wanted
question
test
No milestone
No project
No assignees
1 participant
Notifications
Due date
No due date set.
Dependencies
No dependencies set.
Reference
nspcc-dev/neofs-rest-gw#6
Loading…
Add table
Add a link
Reference in a new issue
No description provided.
Delete branch "%!s()"
Deleting a branch is permanent. Although the deleted branch may continue to exist for a short time before it actually gets removed, it CANNOT be undone in most cases. Continue?
Originally created by @alexvanin on GitHub (Jun 14, 2022).
/authreturns base64 encoded token, e.g.ChB0+OQbVaBLGYnzPP89IXQUEhsKGTVxfQ56a0uQeFmOO63mqykBS1HNpw1rxSgaBgiPAxirAiIhAnLj82Qmdlcg7JtoyhDjJ1OsRFjtmxdXbzrwVkwxWAdWMgQIARAB.WalletConnect expects to sign text string. So the easiest way is to sign this base64 string.
However, gateway and neofs-node now expect signature of binary encoded token. In this case web application should convert base64 => bytes, bytes => string, sign string.
In this issue: double check expected signed value and decide if this scheme should stay or be reworked.
/cc @KirillovDenis @realloc @mike-petrov @masterSplinter01 @fyrchik
@alexvanin commented on GitHub (Jun 15, 2022):
From the front end side, signing string formatted binary messages looks really ugly. Some wallets may hide signing message details, but some don't. Signing binary encoded bearer token looks like this:
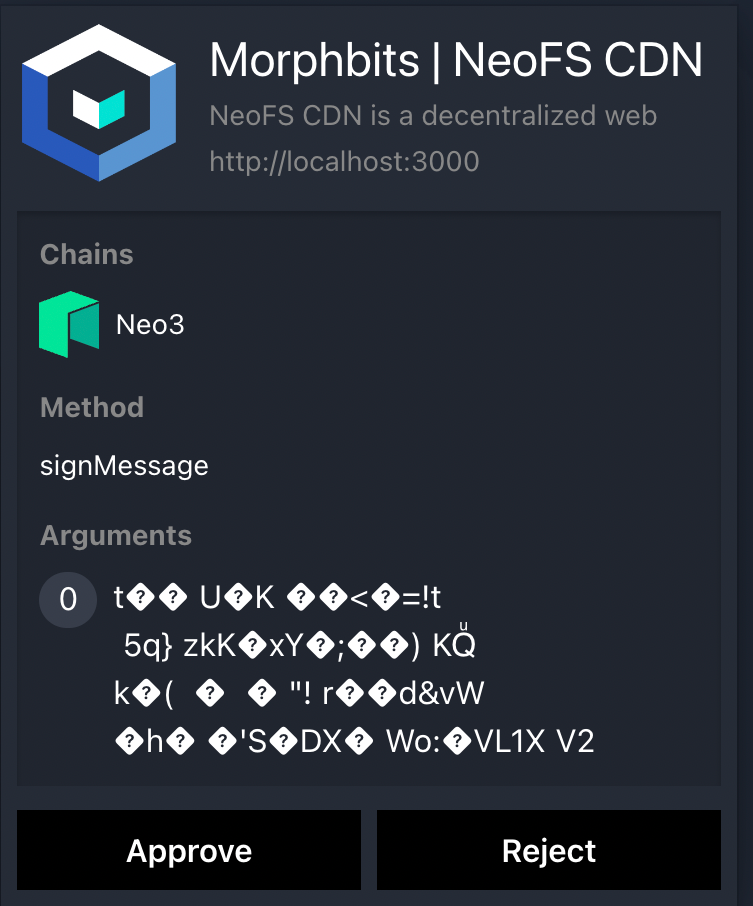
Base64 encoded token will be at least readable.
@fyrchik commented on GitHub (Jun 15, 2022):
I think this is a client issue. Can we have multiple views for signed data? Like this:
As I understand the only problem here is working with protobuf on the javascript side, right?
@alexvanin commented on GitHub (Jun 15, 2022):
This is more like Wallet Connect SDK issue. It allows to sign only strings. Therefore wallet clients, like aero wallet in example above, just prints this string without encoding because, well, it is already a string. Neither front end nor REST Gateway are in control of this output, it is a wallet output.
Since NeoFS wants to provide additional signature type to work specifically with wallet connect, maybe it makes sense to expect signature of string encoded binary data instead of signature of binary data? That's the question I want to discuss there.
@alexvanin commented on GitHub (Jun 16, 2022):
With @mike-petrov we successfully built web app which signs base64 encoded token and REST GW + NeoFS Node use base64 in
Sign/Verifyroutines. We still have issues with signing binary encoded token, though.@alexvanin commented on GitHub (Jun 16, 2022):
After internal meeting we've decided to sign base64 encoded values instead of binary values. I will close this issue when we check that it works fine with all REST Gateway methods.
@alexvanin commented on GitHub (Jun 22, 2022):
NeoFS is going to sign and verify base64 encoded strings of binary data for wallet connect. See:
Closed.